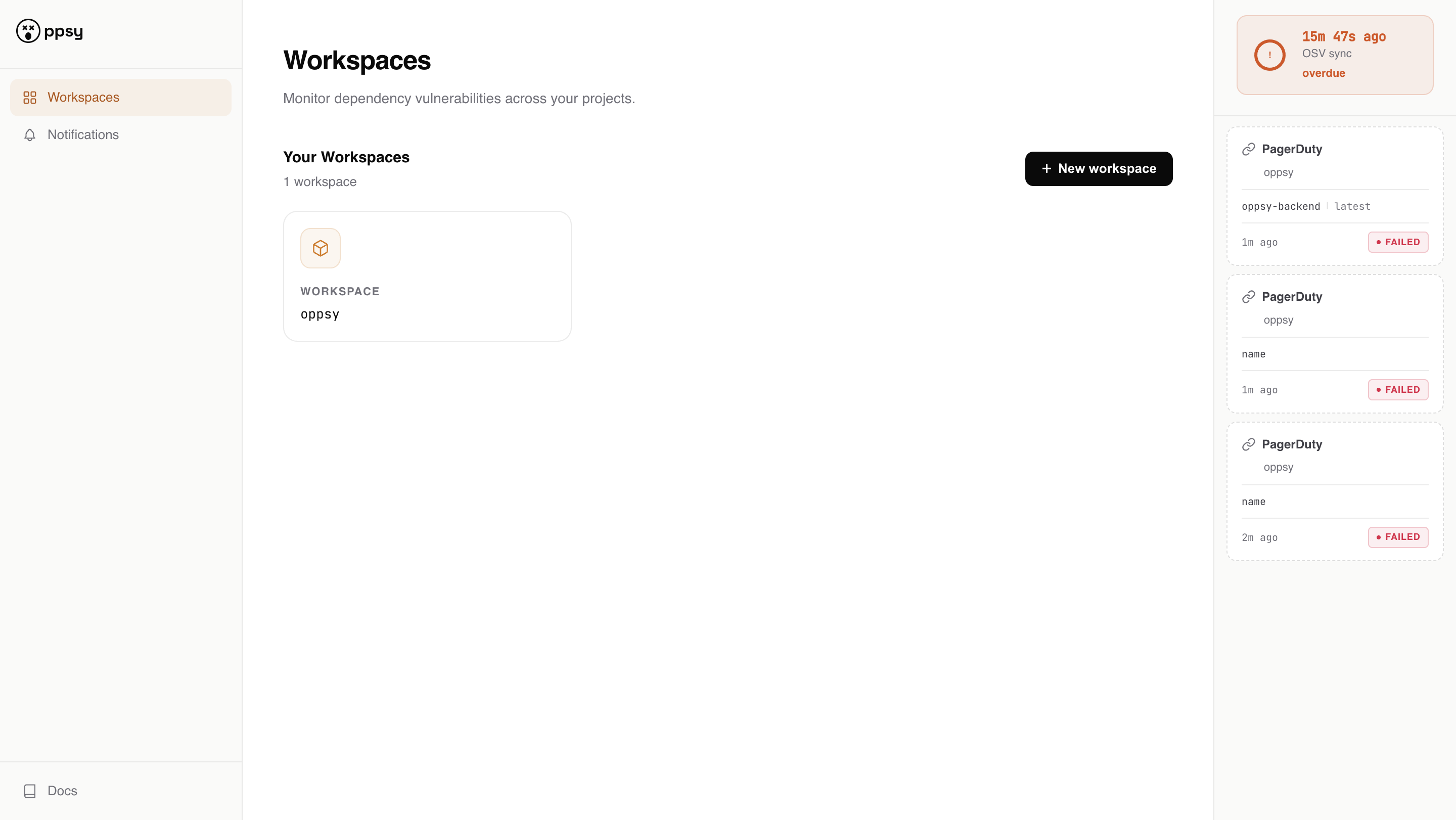
Know when your dependencies are vulnerable
Upload your lock file. We scan it against the OSV database and notify you the moment a new CVE hits your dependencies — via Slack, Discord, Telegram, email, or webhook. Any ecosystem. No agent required.
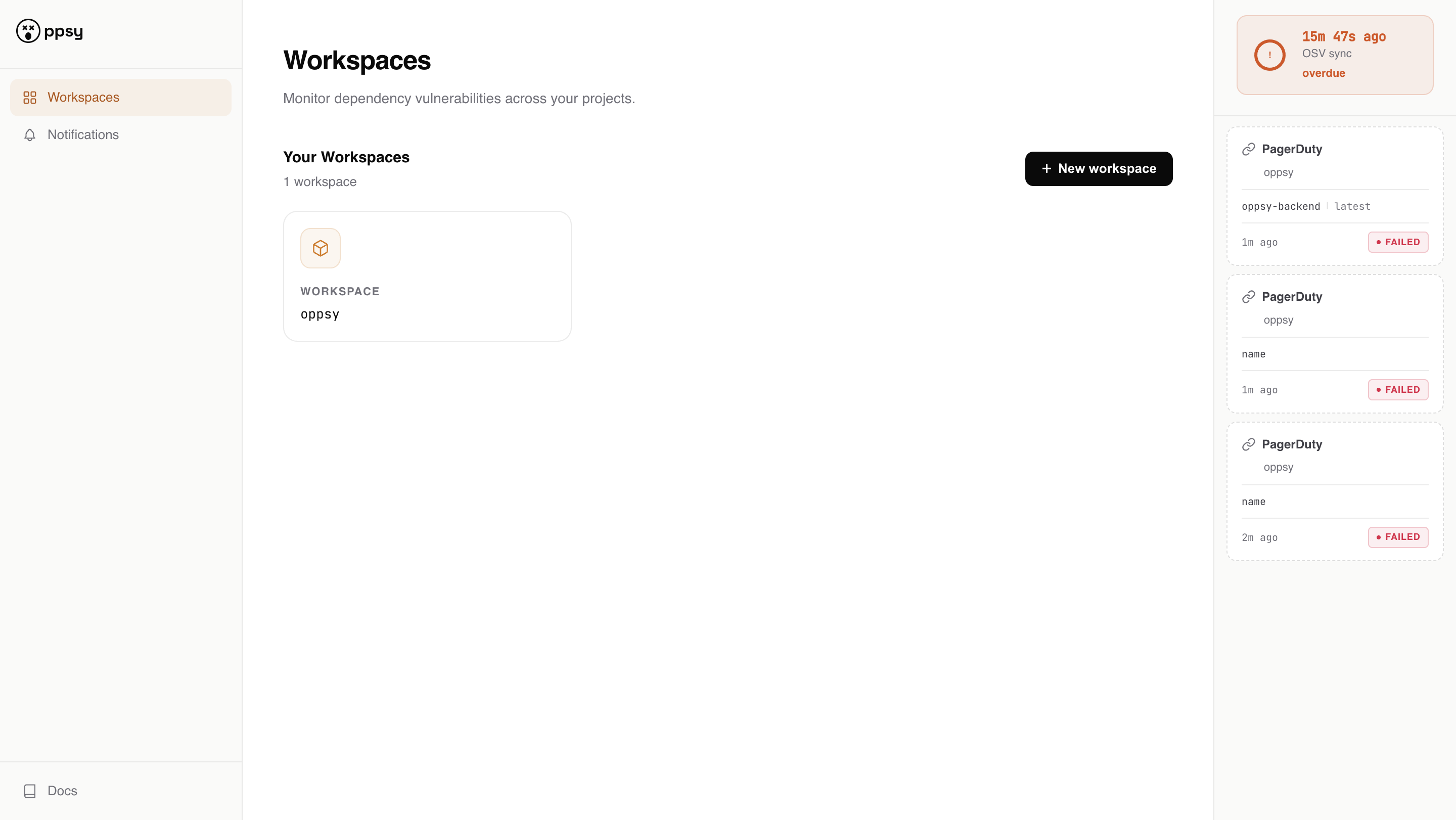
Upload your lock file. We scan it against the OSV database and notify you the moment a new CVE hits your dependencies — via Slack, Discord, Telegram, email, or webhook. Any ecosystem. No agent required.
Supports all major ecosystems
The AI and CI/CD blind spot
Copilot, Cursor, Claude, and every other AI coding tool have a training cutoff. They don't know about CVEs published last week — or last month. When an AI agent adds a dependency, it has no idea whether that package is vulnerable right now. And it compounds: the developers of your dependencies ship with AI too. CI/CD checks helps, but don't eliminate the risk — they only run at build time. Know proactively what you're delivering, not just what you last committed.
express@4.18.2express@4.18.2Features
Slack, Discord, Telegram, email, and signed webhooks. Route alerts to the right channel per workspace — no context switching, no dashboards to check.
Rust, Python, Node.js, Go, Java, Ruby, and more — all covered by the OSV database maintained by Google.
You only upload a lock file — never your source code. We scan dependencies, not your application.
Only get paged for CRITICAL and HIGH — or configure everything. Zero noise, only signal.
Works with any codebase regardless of where it's hosted. Not locked to GitHub, GitLab, or any specific Git provider.
We re-check your lock files every time the OSV database is updated — not just when you upload. New CVE published at 3am? You'll know by morning.
How it works
No agents, no CLI, no GitHub access required.
Drop in Cargo.lock, package-lock.json, poetry.lock, go.sum, or others manually — or push directly from your CD pipeline via the REST API. No agent, no CLI, no Git access required.
We match your dependencies against the OSV database — maintained by Google, covering 30+ ecosystems with continuous updates.
When a new CVE is published that affects your dependencies, you get an alert immediately — through the channel you actually use.
Who it's for
You maintain a library used by thousands. Know the moment a CVE lands in your dependency tree — before your users do.
You run multiple projects. Manually checking lock files before every deploy isn't realistic. Let the alerts come to you.
You don't have a dedicated security engineer. That shouldn't mean zero coverage. Get the same visibility as teams with a full security practice.
Copilot, Cursor, and AI agents write code fast — but they don't monitor for new CVEs. oppsy is the safety net for every dependency they introduce.
FAQ
Cargo.lock, package-lock.json, poetry.lock, uv.lock, go.sum, Maven dependency output, and Gradle lockfiles. More formats are on the roadmap.
We use the OSV database — an open, vendor-neutral vulnerability database maintained by Google. It covers 30+ ecosystems and is updated continuously.
No. You upload a file through the web UI or via REST API. No agent, no CLI, no GitHub App required (though a GitHub App is on the roadmap).
OSV data is synced periodically. Notifications are sent within hours of a new vulnerability being published in the database.
Dependabot works only on GitHub-hosted repositories and supports ~10 ecosystems. Dependabot tracks only the main/master branch. oppsy works with any codebase on any platform, covers 30+ ecosystems, and sends notifications to where you want to (Slack, Discord, Telegram, or any webhook) — not just GitHub PRs.
The alpha is live and open source. Try oppsy today — no sign-up required.